Digital investigations now span cloud environments, mobile devices, remote endpoints, and complex enterprise networks. As cybercrime continues to evolve in sophistication and scale, organizations must rely on advanced forensic technologies to ensure investigative accuracy, maintain evidentiary integrity, and reduce response time. Selecting the right cyber forensics applications is no longer optional—it is foundational to credible incident response and legal defensibility.
TLDR: Cyber forensics applications improve investigative accuracy by preserving digital evidence, automating analysis, and providing defensible reporting. Leading platforms such as EnCase, FTK, Magnet AXIOM, Autopsy, X-Ways Forensics, and Cellebrite each specialize in different areas of digital investigation. Choosing the right tool depends on investigative scope, technical expertise, and legal requirements. Implementing a combination of these tools significantly enhances reliability and efficiency.
Below is a detailed examination of six cyber forensics applications widely recognized for improving investigative precision and supporting defensible digital evidence handling.
1. EnCase Forensic
EnCase Forensic has long been regarded as an industry benchmark in digital investigations. Developed to support law enforcement and corporate investigators, it provides reliable evidence collection and deep forensic analysis capabilities.

Key Strengths:
- Forensically sound disk imaging and data acquisition
- Advanced file signature analysis and recovery
- Robust reporting for courtroom presentation
- Extensive scripting and automation capabilities
EnCase preserves the chain of custody through hash verification and write-blocking techniques. Its automation features help reduce human error, which significantly improves investigative accuracy. Because of its evidentiary reliability, EnCase is frequently used in litigation support and internal investigations.
2. Forensic Toolkit (FTK)
Forensic Toolkit (FTK) is designed for speed and efficiency when processing large volumes of data. Its database-driven architecture allows investigators to quickly index and search evidence without repetitive reprocessing.
Key Strengths:
- High-speed data indexing
- Powerful email and registry analysis
- Memory forensics integration
- Distributed processing for large investigations
FTK excels when handling enterprise-level breaches involving terabytes of information. Its ability to quickly filter relevant evidence reduces investigative delays and ensures that analysts can focus on high-priority artifacts rather than manual sorting.
3. Magnet AXIOM
Magnet AXIOM is widely regarded for its modern interface and its ability to analyze mobile, cloud, and computer data within a unified environment. As digital ecosystems become increasingly interconnected, cross-artifact analysis is essential for accurate conclusions.

Key Strengths:
- Comprehensive mobile device forensics
- Cloud artifact acquisition and analysis
- User-friendly artifact categorization
- Timeline visualization tools
AXIOM automatically organizes artifacts such as chats, browsing history, images, and geolocation data. By presenting findings in intuitive timelines and relationship views, it minimizes interpretation errors and enhances evidentiary clarity.
4. Autopsy
Autopsy is an open-source digital forensics platform built on The Sleuth Kit. Though cost-effective, it is also highly capable when configured properly.
Key Strengths:
- Extensible modular architecture
- Timeline and keyword search functions
- Community-developed plugins
- Cost-effective for smaller agencies and labs
Autopsy is particularly valuable in academic, government, and budget-conscious investigative environments. While it may require more technical expertise than commercial tools, it provides reliable disk analysis and artifact recovery capabilities that meaningfully enhance accuracy when implemented correctly.
5. X-Ways Forensics
X-Ways Forensics is known for efficiency, precision, and minimal system resource consumption. It is often favored by experienced investigators who prioritize control and technical detail.
Key Strengths:
- Lightweight architecture
- Advanced disk and RAID reconstruction
- Manual data inspection capabilities
- Strong hex-level analysis tools
Unlike more automated platforms, X-Ways allows granular manual control. This can be critical when investigating sophisticated attacks where automated parsing may miss subtle indicators of compromise. Its forensic integrity and flexibility directly contribute to investigative reliability.
6. Cellebrite UFED
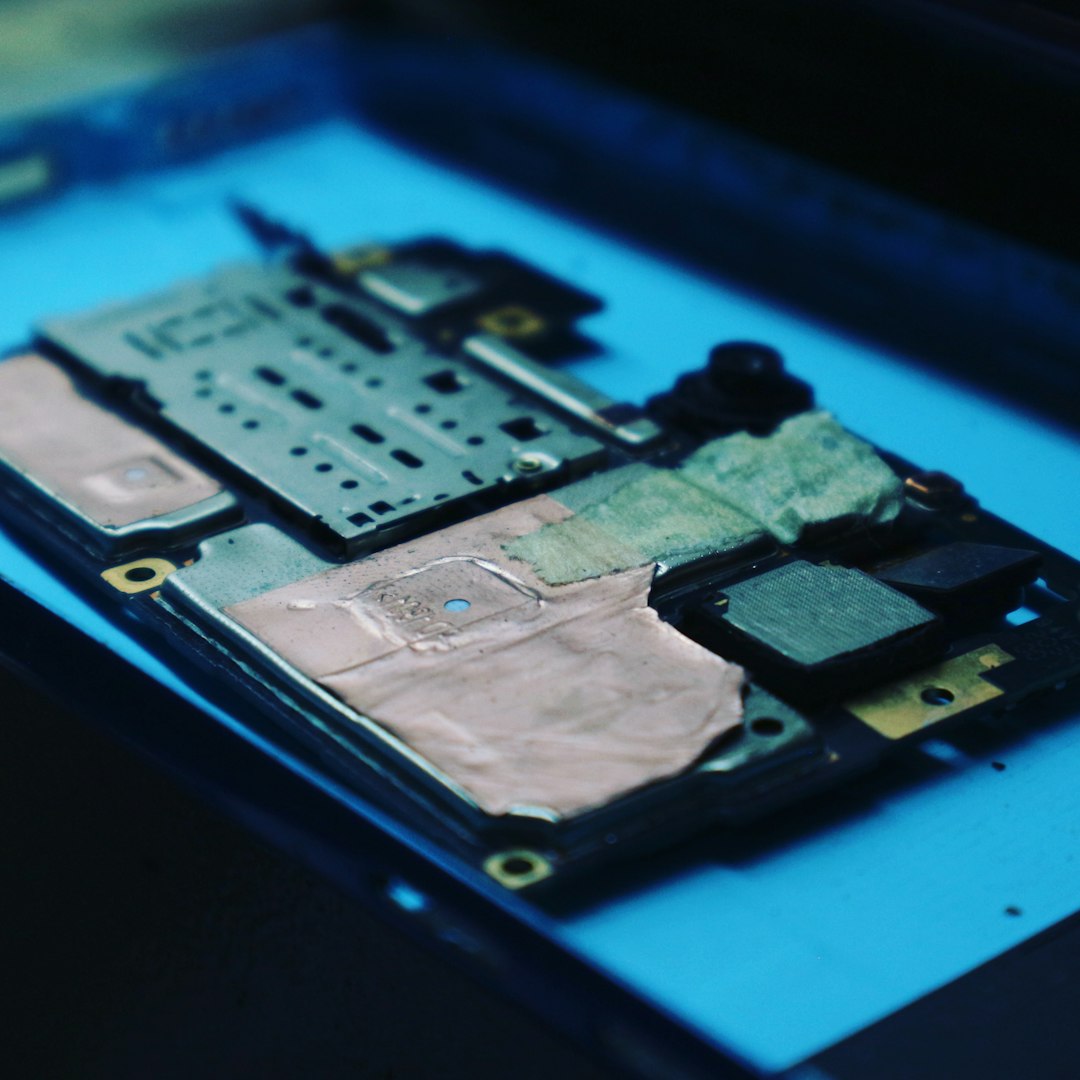
Cellebrite UFED specializes in mobile device acquisition and analysis. Given that smartphones frequently serve as primary evidence sources, mobile forensics is now indispensable in both criminal and corporate investigations.
Key Strengths:
- Logical and physical extraction methods
- Support for a wide range of devices
- Advanced app data recovery
- Password and encryption bypass capabilities (where legally authorized)
Cellebrite enhances accuracy by enabling deep device-level access and comprehensive artifact reconstruction. Its frequent updates ensure compatibility with evolving operating systems, which is essential in contemporary investigations.
Comparison Chart of Leading Cyber Forensics Apps
| Tool | Primary Focus | Best For | Strength in Accuracy |
|---|---|---|---|
| EnCase | Disk and system analysis | Legal and law enforcement investigations | High evidentiary reliability and reporting |
| FTK | Large-scale data indexing | Enterprise breach analysis | Fast data filtering and structured processing |
| Magnet AXIOM | Mobile and cloud forensics | Cross-platform investigations | Artifact correlation and visual clarity |
| Autopsy | Open-source disk forensics | Academic and mid-budget labs | Flexible modular investigation |
| X-Ways | Manual precision analysis | Advanced forensic practitioners | Granular control and RAID reconstruction |
| Cellebrite | Mobile device extraction | Smartphone investigations | Deep mobile artifact recovery |
How These Tools Improve Investigation Accuracy
Accuracy in cyber forensics depends on more than software capabilities—it requires procedural rigor, validated methodologies, and evidence integrity. These applications support accuracy through:
- Forensic Imaging: Bit-by-bit duplication prevents alteration of original data.
- Hash Verification: Cryptographic hashes confirm evidence authenticity.
- Artifact Correlation: Automated cross-referencing reduces oversight.
- Visualization: Timelines and dashboards clarify event sequences.
- Comprehensive Logging: Audit trails document investigative actions.
When combined with trained personnel and defensible methodology, these tools significantly reduce investigatory error, strengthen legal admissibility, and improve confidence in findings.
Conclusion
Cyber investigations demand precision, transparency, and defensibility. The six applications outlined above represent some of the most reliable solutions currently available to digital forensic professionals. Whether addressing corporate data breaches, insider threats, criminal investigations, or regulatory compliance audits, selecting the appropriate forensic software directly impacts investigative accuracy.
No single tool satisfies every investigative need. However, a well-equipped digital forensics team often integrates multiple platforms—leveraging EnCase for evidentiary integrity, FTK for large-scale indexing, Magnet AXIOM for artifact correlation, Autopsy for modular flexibility, X-Ways for granular inspection, and Cellebrite for mobile extraction.
In a threat landscape defined by complexity and rapid change, dependable forensic applications remain indispensable. Institutions that invest in robust forensic capabilities position themselves to respond decisively, preserve evidence effectively, and maintain credibility in both technical and legal environments.