The internet feels instant and direct. You type a website. You hit enter. Boom. The page loads. But behind that simple click is a complex dance of systems talking to each other. One of the quiet heroes in this dance is the proxy server. It sits in the middle. It carries messages. It protects. It controls. And today, it is shaping how digital infrastructure works across the world.
TLDR: Proxy servers act as middlemen between users and the internet. They improve security, boost speed, manage traffic, and protect privacy. Businesses, schools, and governments rely on them to control and optimize online activity. As the internet grows, proxies are becoming a core piece of modern digital infrastructure.
What Is a Proxy Server?
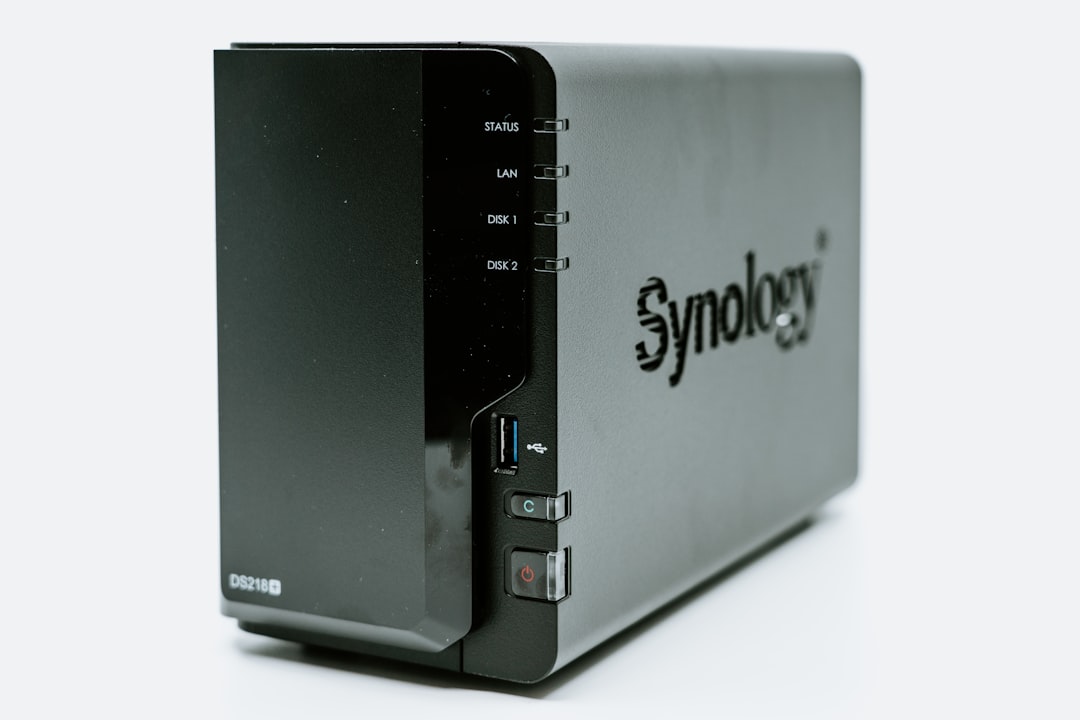
A proxy server is simple in concept. It is an intermediary. Instead of your device talking directly to a website, it talks to a proxy. The proxy then talks to the website for you.
Think of it like ordering food through a waiter. You do not walk into the kitchen. The waiter carries your request. Then the waiter brings the food back.
In the digital world, the proxy is the waiter.
- Your device sends a request to the proxy.
- The proxy forwards the request to the website server.
- The website responds to the proxy.
- The proxy sends the data back to you.
Simple. But powerful.
Why Do Proxy Servers Matter?
At first glance, proxies may seem like extra steps. Why not connect directly?
Because that “extra step” creates control.
And control is everything in digital infrastructure.
Here is what proxies make possible:
- Security filtering
- Content control
- Load balancing
- Caching for speed
- Anonymity and privacy
- Traffic monitoring
Without proxies, managing large networks would be chaotic. Businesses would struggle. Schools could not filter content easily. Enterprises would face higher cybersecurity risks.
Proxies give administrators a control panel for the internet.
Security: The First Line of Defense
Cybersecurity threats are everywhere. Malware. Phishing. Data theft. Ransomware.
A proxy server acts like a guard at the gate.
It can:
- Block suspicious websites.
- Filter harmful downloads.
- Inspect traffic patterns.
- Detect unusual behavior.
Many companies use forward proxies to protect employees. Workers connect to the internet through the proxy. The proxy inspects outgoing requests. If something looks dangerous, it stops it.
This reduces the attack surface. It also stops users from accidentally visiting risky sites.
On the other side, organizations use reverse proxies to protect their own servers. Instead of exposing internal systems directly, the reverse proxy handles incoming traffic. This hides the real structure of internal networks.
Hackers see the proxy. Not the real server.
Privacy and Anonymity
When you browse directly, websites can see your IP address. This reveals your approximate location and internet provider.
A proxy can hide that.
When you use a proxy:
- The website sees the proxy’s IP address.
- Your real identity stays hidden behind it.
This is why proxies are popular for:
- Privacy-focused browsing
- Research and journalism
- Bypassing regional restrictions
- Web scraping and data collection
However, not all proxies guarantee full privacy. Some log traffic. Some modify data. Trust matters.
In digital infrastructure, privacy controls are becoming critical. Regulations like GDPR and other data laws push companies to handle user data more responsibly. Proxies help create structured control over how traffic flows.
Speed and Performance: The Hidden Boost
Proxies are not just about blocking things. They also make the internet faster.
How? Through something called caching.
A caching proxy saves copies of frequently accessed content. If multiple users request the same website resource, the proxy can serve it directly. No need to fetch it again from the original server.
This means:
- Faster load times
- Reduced bandwidth usage
- Lower server strain
- Better user experience
In large companies with thousands of employees, this makes a big difference. It reduces external traffic. It improves internal efficiency.
On a global scale, caching supports modern content delivery strategies. It works hand in hand with CDNs (Content Delivery Networks). Together, they reduce latency and improve reliability.

Types of Proxy Servers
Not all proxies do the same job. Let’s break down the main types in a simple way.
| Type | Where It Sits | Main Purpose | Common Use Case |
|---|---|---|---|
| Forward Proxy | Between user and internet | Controls outgoing traffic | Corporate networks |
| Reverse Proxy | In front of web servers | Protects and balances incoming traffic | Web applications |
| Transparent Proxy | Between user and web, unnoticed | Filters content without user setup | Schools, public WiFi |
| Anonymous Proxy | Between user and internet | Hides IP address | Private browsing |
| High Anonymity Proxy | Between user and internet | Hides IP and proxy identity | Research, automation |
Each type serves a different architectural need. Together, they form a flexible toolkit for network design.
Load Balancing and Scalability
Imagine a website gets millions of visitors per hour. One server cannot handle that alone.
This is where reverse proxies shine.
A reverse proxy can distribute traffic across multiple servers. This is called load balancing.
- Server A handles part of the traffic.
- Server B handles another part.
- Server C stays ready as backup.
If one server fails, the proxy reroutes traffic automatically. Users may never notice.
This makes systems:
- More reliable
- More scalable
- More efficient
As cloud computing grows, load balancing becomes essential. Proxies play a central role in managing these distributed systems.
Enterprise Control and Monitoring
Companies need visibility. They must understand how employees use the internet. Not to spy. But to protect resources and ensure productivity.
Proxies allow:
- Traffic logging
- Usage analytics
- Policy enforcement
- Access restrictions
For example:
- Block social media during work hours.
- Prevent file-sharing site access.
- Allow only approved cloud platforms.
This structured management shapes internal digital ecosystems. It ensures compliance with laws and industry regulations.
In regulated industries like finance and healthcare, this level of control is not optional. It is required.
Proxies in the Age of Cloud and Edge Computing
Digital infrastructure is changing fast.
We have:
- Cloud-native applications
- Microservices architectures
- Edge computing systems
- Remote workforces
All of these increase traffic complexity.
Proxies help manage this complexity.
In microservices environments, internal services communicate constantly. Specialized proxies, often called service proxies, manage communication between services. They handle security, routing, and monitoring.
At the edge, proxies help process data closer to the user. This reduces delay. It improves performance for real-time apps like video calls and online gaming.
The more distributed systems become, the more important intermediaries become.
Challenges and Risks
Proxies are powerful. But they are not perfect.
Some risks include:
- Single point of failure if misconfigured
- Performance bottlenecks
- Privacy concerns with logging
- Abuse for malicious anonymity
Free public proxies, for example, can be dangerous. They may inject ads. They may track users. They may even steal data.
This is why enterprise proxies require careful configuration and strong security practices.
Infrastructure must be monitored. Updated. Tested.
A poorly managed proxy can become a weak link.
The Future of Proxy Servers
As the internet evolves, proxy servers are evolving too.
We are seeing:
- AI-driven traffic analysis
- Smarter threat detection
- Zero trust network integration
- Cloud-native proxy services
In zero trust models, no request is automatically trusted. Every connection is verified. Proxies are ideal enforcement points for this approach.
They check identity. Device status. Permissions.
Nothing moves forward without validation.
This shifts proxies from simple intermediaries to intelligent gatekeepers.
Why They Truly Shape Digital Infrastructure
Modern digital infrastructure depends on:
- Security
- Scalability
- Speed
- Reliability
- Compliance
Proxy servers contribute to all five.
They stand in the middle of digital communication. Not as obstacles. But as orchestrators.
Without proxies:
- Traffic would be harder to control.
- Cybersecurity defenses would weaken.
- Scaling web services would be more complex.
- Privacy options would shrink.
They may not be visible to everyday users. But they are fundamental building blocks of the modern internet.
Like traffic lights in a busy city, proxies regulate flow. They prevent collisions. They keep things moving smoothly.
As our world becomes more connected, more cloud-based, and more data-driven, these quiet intermediaries will continue shaping how the digital world functions.
And next time you load a website, remember: you are probably not talking to it directly.
You are speaking through a well-organized, invisible middle layer.
A proxy server.